


What’s the Difference Between Standard, Industrial, and Enterprise Data Storage?
Standard, industrial, and enterprise-class drives are different classes of hard disk drives (HDDs) or solid-state drives (SSDs)—each designed for specific use cases and environments. Under the conditions for which they were created, users can expect reliable...
Key Takeaways from the Recent LastPass Cybersecurity Breaches
Our federal government has repeatedly pointed to data breaches as a serious matter of national security, given the wide-ranging impacts attacks can have on our shared infrastructure, private companies, and individual consumers. Despite increased attention on...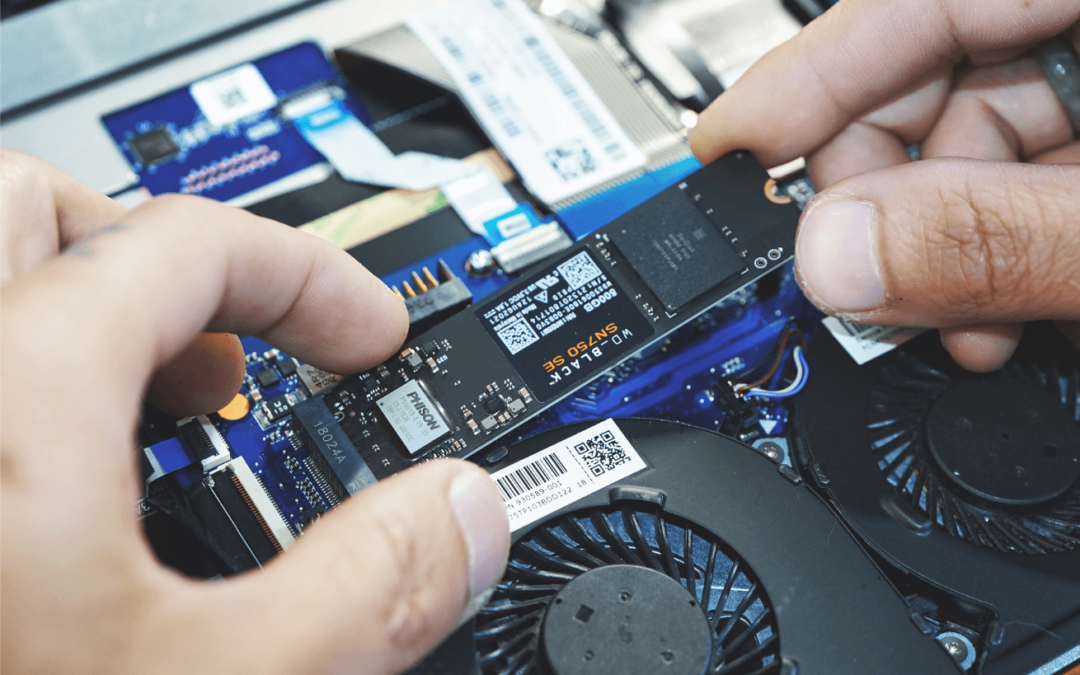
How to Choose the Right Data Storage for Your Application
In our latest post, we described key differences between standard, industrial, and enterprise-class SSDs. SSD form factors, performance in extreme conditions, the number of DWPDs (drive writes per day) under warranty, the length of the drive’s warranty, and advanced...
With CSfC Listing, There’s No Cyber Waiver for Storage Needed Here!
Back in the early aughts, the NSA created a program called CSfC – or Commercial Solutions for Classified. As we explain in our post “Innovation, Integrity & Affordability: Why CSfC Matters,” this program “allows commercial off-the-shelf technology to be used in...

Recent Comments