Moving data in an air-gapped network can be difficult due to the intensive protocols required to protect sensitive data during transit. As we note in a previous post, an air gapped computer or air-gapped network is one that has been siloed from others.
Air-gapping creates a highly secure environment in which data is well-protected. One would need to be in the same physical space to breach air gapped computers. All these security measures mean that data housed in air gapped systems can be somewhat difficult for authorized users to access.
Air-gapped computers are physically isolated. To protect against malware and other attempts to steal data, only people who have physical access to air-gapped systems can utilize them.
Such environments lack any of the hardware that would make internet connectivity and virtual access possible. Many air-gapped systems are housed in high-security facilities like SCIFs and SAPFs. In some cases, this means that commercial software and hardware cannot be used.
As such, air-gapping presents several challenges regarding moving data within an air-gap environment and moving data out of that environment. In this post, we consider data transfer challenges in an air-gapped environment.
What Exactly are Air Gaps?

Air gaps are physical or conceptual separations between devices that prevent unauthorized access to data at rest. Data transmitted between devices in a physical air gapped system can only be shared manually by authorized users.
In a logical or conceptual air gap, software is used to silo devices. Antony Adshead explains in an article for Computer Weekly. Adshead writes that a logical or conceptual air gap is created through “a protection in software.” This software protection “isolates secondary site locations from production and primary backup environments.
Some air gapped systems are a hybrid model. In these hybrid models, computers are physically isolated from one another, but can be connected to a network if needed.
Is Physical or Logical Air Gapping More Secure?

Physical separation creates the most secure air gapped network. However, some users opt for logical air gapping because it is easier to grant access and transfer data.
The term “air gapping” has been used casually to describe any system without a Wi-Fi connection. For example, one might refer to a cell phone, laptop or tablet with Bluetooth connectivity turned off as “air gapped.” However, true air gapped devices are not just disconnected. They are intentionally and systematically isolated from the internet and from each other to protect sensitive data.
Physical air-gapping is a common security measure used to protect sensitive data housed in critical systems. For example, air gapping is common practice for industrial control systems (ICS), military computer systems and financial computer systems.
How Can You Transfer Data in an Air Gapped System?

As noted above, physically air gapped systems are highly secure environments in which devices are not connected to the internet. When critical systems are at risk, air gapped computers are siloed from each other, and their storage facility is carefully guarded.
Though air gapping is commonly used to protect data at rest, data transfer is necessary in certain cases. To transfer data in a physically air gapped system, one must download data onto secure drives. These removable drives are inserted directly into the air gapped computer in question.
Oftentimes, multiple authentication steps must be taken to access the data and transfer it to a device. There might also be limitations on how the data is encrypted and formatted during transfer.
These measures belie the fundamental challenges of transferring data within an air gapped computer system. Downloading data from an air gapped computer to a drive can be complex and time-consuming.
Transferring Data from One Siloed Device to the Next (Internal Transfer)
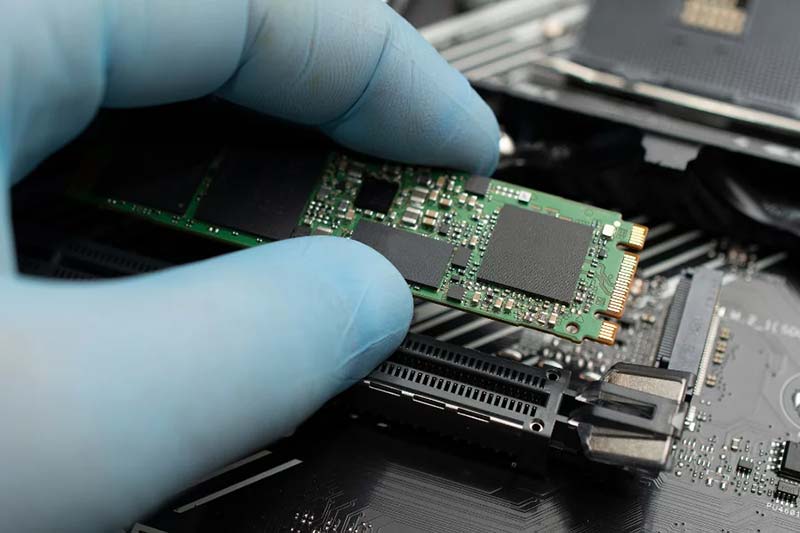
Downloading data onto a removable drive is not always the most practical way to transfer data from one device to another. If regular data transfer is needed in an air gapped system, one might opt for the hybrid model described above. With a hybrid model of air gapping, computers can be connected to each other through a WAN or Wide Area Network. This enables swift but secure internal data transfer.
Whether one chooses to transfer sensitive data over the network, or download that data onto removable drives, special measures must be taken. Data should be scanned for viruses, cleaned, reviewed by an SME, and encrypted before it is transferred across the air gapped network. To access the encrypted data, MFA, TPI and other authentication measures should be required.
Transferring Data from One Network to Another (External Transfer)

Of course, there are situations in which data must be transferred from one network to another. External data transfers — or Assured File Transfers — require a more complex system of checks and balances. When dealing with highly sensitive data, an ISSM or Information Systems Security Manager is assigned to oversee the transfer.
Many of the steps described above — i.e., scanning, cleaning, reviewing and encrypting — must be taken to download such sensitive data. However, the protocol by which one physically transfers sensitive data to another site after downloading it onto an encrypted drive is far more intense.
The drive in question must be escorted by approved personnel. To gain access once the data is transferred from one network to the next, additional security measures must be taken.
Still Have Questions About Transferring Data in Air Gapped Environments?

If you still have questions about securely transferring data within or beyond an air gapped network, stay tuned for additional posts on the subject.


Recent Comments