The term cryptography refers to the art and science of keeping data secret. Ever since writing was developed, people have tried to conceal the information it contained. According to the Encyclopedia Britannica, “Examples survive in stone inscriptions, cuneiform tablets, and papyruses showing that the ancient Egyptians, Hebrews, Babylonians, and Assyrians all devised proto-cryptographic systems both to deny information to the uninitiated and to enhance its significance when it was revealed.”
Encryption, Decryption, and Cryptographic Keys
In cryptography, encryption is the process of encoding information using an algorithm known as a cipher in conjunction with a secret piece of information in the form of a cryptographic key. Historically, the data to be protected was textual in nature, so the unencrypted text was called plaintext and its encrypted counterpart was known as ciphertext. The complement to encryption is decryption, which employs a decryption algorithm in conjunction with a key to convert the ciphertext back into plaintext.
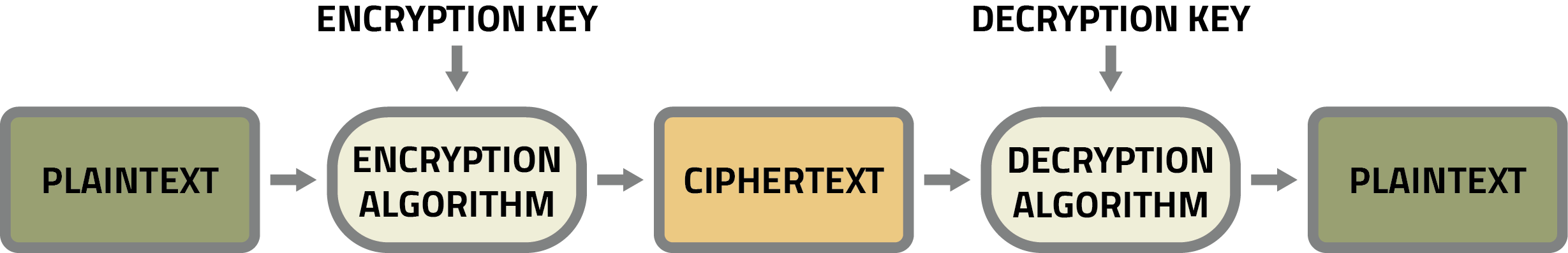
Today, plaintext has expanded beyond human-readable documents to encompass any data, including binary files, in a form that can be viewed or used without requiring a key or other decryption device. Similarly, ciphertext has expanded to cover the encrypted version of any form of plaintext.
A cryptographic key is typically a string of letters, numbers, and non-alphanumeric symbols (!@#$%&^ etc.) that — when processed through a cryptographic algorithm — can encode or decode cryptographic data. In the case of symmetric cryptography, the same key is used for both encryption and decryption. By comparison, in the case of asymmetric cryptography, separate keys are used for encrypting and decrypting, where these keys are known as the public key and private key, respectively.
How Cryptic
Hundreds of symmetric key algorithms exist, but many of them have been cracked by hackers, including the Data Encryption Standard (DES) and 3DES, which — as its name suggests — involves applying the DES algorithm three times to each block of data. The most widely used symmetric key algorithm at the time of this writing is the Advanced Encryption System (AES), which became a standard when it was approved by the National Institute of Standards and Technology (NIST) in 2001. When you see references to AES-128 and AES-256, the last three digits refer to the length of the key. The longer the key, the harder it is to crack using a brute force attack.
The two main asymmetric key algorithms are RSA (whose name was derived from the first letters of the family names of its inventors: Ron Rivest, Adi Shamir, and Leonard Adleman) and ECC (which stands for Elliptic Curve Cryptography). At the time of this writing, RSA is the most widely used asymmetric encryption algorithm.
Although asymmetric key algorithms provide the public-private key advantage, they require much more computational horsepower than do their symmetric key counterparts. Thus, many applications employ a hybrid approach in which the bulk of the data is encrypted and decrypted using a symmetric key algorithm while the identities of the players are confirmed using an asymmetric key algorithm.
Don’t Forget the Specifications and Standards
Technology is interesting, but it’s insufficient on its own. What is required are proven specifications and standards that have been developed and agreed upon by trusted bodies.
Different standards are applicable to different applications, situations, and use cases, such as whether the data to be protected is at rest, in use, or in transit. Data at rest (DAR) refers to data that is physically housed in a storage device such as a solid-state drive (SSD). Data in use refers to active data that is being accessed and manipulated by a software program and is stored in a non-persistent digital state, typically in the computer’s random-access memory (RAM) or in the caches and registers associated with the central processing unit (CPU). Data in transit (a.k.a. data in motion or data in flight) is information that is flowing through a network, including private corporate networks and public networks such as the internet.
Let’s focus on DAR as an example. Federal Information Processing Standards (FIPS) are standards and guidelines for Federal computer systems that are developed by NIST in accordance with the Federal Information Security Management Act (FISMA) and that are approved by the Secretary of Commerce. A FIPS 197 certification guarantees that the AES cryptographic algorithm has been implemented correctly and has sufficient entropy. A FIPS 140-2 certification assures that hardware encryption engine (EE) in a self-encrypting drive (SED) has been properly designed and secured. Furthermore, a FIPS 140-2 L2 (“Level 2”) certification — which is required for most DAR applications — ensures that there is visible evidence of any attempt to physically tamper with the drive. To be acceptable for use by the Federal Government, a DAR solution must be NIST-validated and FIPS-certified.
There are also organizations like the Trusted Computing Group (TCG), which is a consortium of technology companies whose goal is to promote and implement trusted computing concepts. The TCG’s Opal Storage Specification defines features of data storage devices (such as SSDs) that enhance their security. TCG Opal manages the encryption and decryption of information within the storage device itself, thereby enabling fast encryption/decryption and minimizing the risk of data leakage without undermining system performance.
And we must also not forget the National Information Assurance Partnership (NIAP), which is responsible for the U.S. implementation of the Common Criteria (CC) — an international standard (ISO/IEC 15408) for IT product security certification.
Don’t Panic!
As you’ve probably gathered by now, a lot of things are involved when it comes to securing your systems against cyberattack. At DIGISTOR, we specialize in helping military and government agencies and commercial entities of all sizes find the right secure storage solution to secure their DAR. With a wide range of secure storage offerings, from bare drives to removable solutions to Commercial Solutions for Classified (CSfC)-ready SSDs, we can assist with specifying the appropriate storage devices to secure your important data. If you have any questions as to how any of these cryptographic standards and technologies might apply to your own data security requirements, please feel free to contact us.
Additional Resources
Whitepaper: Building a Citadel of Trust in a Zero Trust World
Whitepaper: Is Your Data at Rest (DAR) Truly Secure?
Blog: Classified Information and Data at Rest (DAR)
Article on EEJournal.com: Secure Your Data at Rest, Stupid!

Recent Comments