Check out the Center for Internet Security (CIS), which has a wealth of cybersecurity resources. (Other organizations such as the Cybersecurity & Infrastructure Security Agency, or CISA, have resources and assessments of their own.) Formed in 2000, CIS is a community-driven nonprofit organization. Its mission is to make the connected world a safer place by creating best practices for people and organizations of all stripes to protect themselves against pervasive cyberthreats.
CIS plays an important role in forming security policies and decisions by maintaining the CIS Controls and CIS Benchmarks, which are globally recognized best practices for securing IT systems and data. They hosts the Multi-State Information Sharing and Analysis Center (MS-ISAC), which has representation from all 50 states and 2500 organizations. CIS also hosts the Elections Infrastructure Information Sharing and Analysis Center to support elections agencies in their quest to protect elections from cyberthreats.
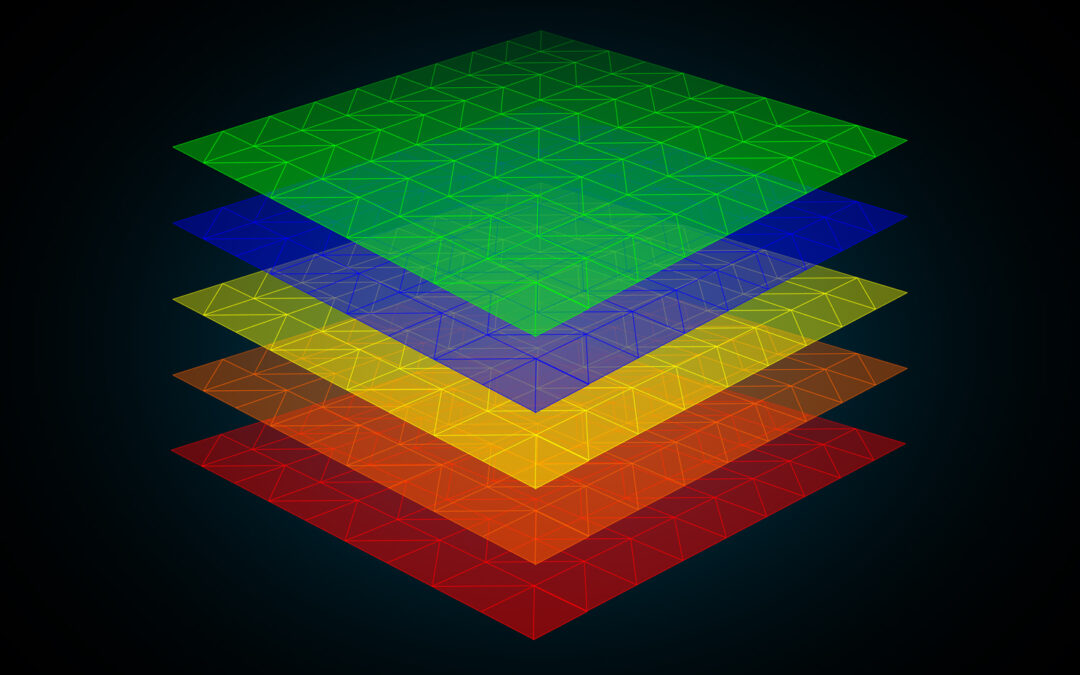
As part of their mission, CIS and MS-ISAC cybersecurity professionals analyze risks and alert members to current online security threats, which are categorized as follows:
- Low (Green). No unusual activity exists beyond the normal concern for known hacking and viruses or other malicious activity.
- Guarded (Blue) indicates an increased risk of hacking, virus, or other malicious activity. The potential exists for maliciousness (or there may be known threats) yet no significant impact has occurred.
- Elevated (Yellow) means there is a significant risk from increased hacking, virus, or other malicious system-compromising activity. A moderate level of damage has been detected, or the possibility of significant damage is high.
- High (Orange) denotes a high risk of increased hacking, virus, or other malicious activity aimed at core infrastructure. A high level of damage or disruption is likely, or severe damage or disruption is possible.
- Severe (Red) indicates a severe risk of hacking, virus, or other malicious activity resulting in widespread outages and/or significantly destructive compromises to systems with no known remedy or debilitates one or more critical infrastructure sectors. At this level, vulnerabilities are being exploited with a severe level or widespread level of damage or disruption of Critical Infrastructure Assets.
So how is an alert level determined? Using the concepts of Criticality (the attack target), Lethality (the likelihood for damage), System Countermeasures (host-based preventative measures that are in place), and Network Countermeasures (network-based preventative measures that are in place), an equation has been developed:
Severity = (Criticality + Lethality) – (System Countermeasures + Network Countermeasures)
Each of the four variables is assigned a value from 1 to 5. In the case of Criticality, for example, a home user has a target value of 1, while a core service such as a critical router, firewall, VPN, IDS system, DNS server, or authentication server has a target value of 5.
As a result, the severity level can range between -8 to +8, where -8 to -5 equates to Low/Green, -4 to -2 equates to Guarded/Blue, -1 to +2 equates to Elevated/Yellow, +3 to +5 equates to High/Orange, and +6 to +8 equates to Severe/Red.
Don’t Forget Data at Rest
The aforementioned MS-ISAC is a “round-the-clock cyber threat monitoring and mitigation center for state and local governments” operated by CIS under a cooperative agreement with the Cybersecurity and Infrastructure Security Agency (CISA) under the auspices of the Department of Homeland Security (DHS).
The threat levels defined by CIS and determined by MS-ISAC are used to describe current online security threats at national and international levels, but organizations can develop similar schemes for internal use focused on their own environments.
One vital point for these organizations to include in their evaluations is securing their data at rest (DAR), which is inactive data physically housed in a storage device, such as a solid-state drive (SSD). Many recent security breaches and data loss incidents have been traced to insider threats in the form of unauthorized access to sensitive information, or to computers and/or their drives being mislaid or stolen, which highlights the importance of securing stored information.
At DIGISTOR, we specialize in helping military and government agencies and commercial entities of all sizes find the right encrypted storage solution to secure their DAR. With a wide range of secure storage offerings, from bare drives to removable solutions to Commercial Solutions for Classified (CSfC)-ready SSDs, we can assist with specifying the appropriate storage devices to secure your important data. If you have any questions as to securing DAR might apply to your own data security requirements, please feel free to contact us.
Additional Resources
Whitepaper: Building a Citadel of Trust in a Zero Trust World
Whitepaper: Is Your Data at Rest (DAR) Truly Secure?
Blog: Classified Information and Data at Rest (DAR)
Blog: An Overview of Encryption Standards and Technologies
Article on EEJournal.com: Secure Your Data at Rest, Stupid!

Recent Comments