Previous blogs highlighted headline-making cyberattacks. Of course, there’s the infamous 2020 SolarWinds attack: the Russian Foreign Intelligence Service injected malicious code into network management software, infecting thousands of users in federal agencies like the Pentagon, State Department, Department of Energy, National Nuclear Security Administration, and Treasury.
In early 2018, the silicon chip behemoth Taiwan Semiconductor Manufacturing Company (TSMC) fell prey to ransomware. A new computer infected by the WannaCry virus was brought into a TSMC manufacturing plant. An unsuspecting employee connected the machine to the plant’s intranet before the IT department could make sure the machine was clean. The virus ultimately impacted more than 10,000 computers and fabrication machines. The price tag to TSMC ended up around $200M.
A “supply chain” attack called the Zombie Zero happened in 2014: A contract manufacturer worked with a hacker organization to load compromised firmware into handheld barcode scanners. When the scanners were connected to networks of victim organizations, including several Fortune 100 companies, they extracted every piece of scanned data.
In addition to external attack vectors, many security breaches and data loss incidents are traced to insider threats in the form of unauthorized access to sensitive information, or to computers and/or their drives being mislaid or stolen.
Zero Trust Cybersecurity
An evolving approach to cyberthreats is to adopt a zero trust (ZT) cybersecurity model. This model is a mindset that behaves as if the threat is already present. Perimeter security is no longer sufficient to protect data.
The zero trust model has evolved since its coinage in 1994 by Stephen Marsh. Forrester Group’s John Kindervag helped popularize the model over 10 years ago and it has become a driving force for organizations create data protection infrastructure.
A November 10, 2021 C4ISRNET article—Pentagon ‘Zero Trust’ Cyber Office Coming in December—noted that the Pentagon is going to formally launch a new office dedicated to accelerating the adoption of a zero trust. This is a big milestone for the adoption of the zero trust security model.
Seven Pillars of Zero Trust
A recent C4ISRNET-sponsored conference featured a talk by David McKeown, Deputy DoD CIO for Cybersecurity/Chief Information Security. McKeown laid out seven pillars of zero trust environments, which are as follows. (I believe Forrester’s model has also evolved to have seven similar pillars.)
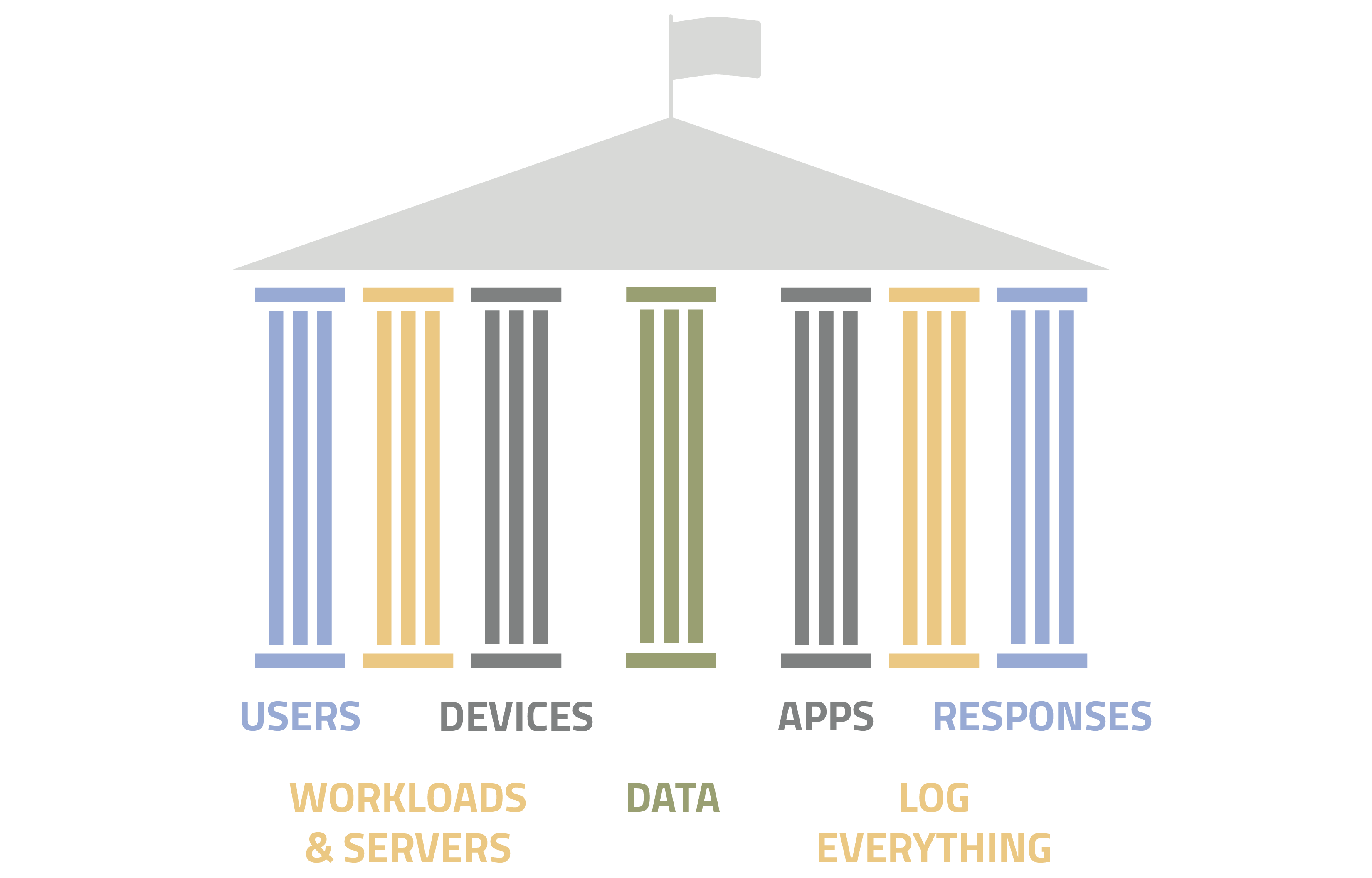
- Data needs to be secure in and of itself (encrypted, eg) with permission-based access
- Users need to be authenticated and their access controlled
- Ensure that devices are secure (or if not, provide lower-level environment access)
- Workloads and servers need to be segmented to minimize risk that multiple applications and data are exposed
- Segment applications themselves so they cannot affect each other
- Log everything in the environment—and analyze.
- Orchestrate and automate responses; codify human-based processes
Securing DAR is Critical
As I’ve noted before, a key aspect of a zero trust environment is to secure Data at Rest (DAR) since data access is exactly the reason most cyberattacks are created. Using SSDs equipped with the following capabilities is a big step to securing DAR:
- A certified hardware encryption engine (EE) to facilitate encryption as data is written and decryption when reading the drive,
- with an on-drive data encryption key (DEK) to reduce key management issues,
- authorization acquisition (AA), to release the DEK to the encryption engine,
- multi-factor authentication (MFA), to goes beyond single password security
- and pre-boot authentication (PBA), which requires authentication to authorize the computer to boot up.
At DIGISTOR, we specialize in helping military and government agencies and commercial entities of all sizes find the right encrypted storage solution to secure their DAR. With a wide range of secure storage offerings, from bare drives to removable solutions to Commercial Solutions for Classified (CSfC)-ready SSDs, we can assist with specifying the appropriate storage devices to secure your important data. If you have any questions as to securing DAR might apply to your own data security requirements, please feel free to contact us.
Additional Resources
Whitepaper: Building a Citadel of Trust in a Zero Trust World
Whitepaper: Is Your Data at Rest (DAR) Truly Secure?
Blog: Classified Information and Data at Rest (DAR)
Blog: An Overview of Encryption Standards and Technologies
Blog: Cybersecurity Threat Levels: What Do You Know?
Blog: It’s All About Speed: PCIe Gen 4
Blog: CISOs: Maintaining Cybersecurity at a Global Scale
Article on EEJournal.com: Secure Your Data at Rest, Stupid!


Recent Comments